VPSGuard
ML-first VPS log security analyzer that detects distributed attacks like botnets and credential stuffing that rule-based tools miss.
Tech Stack
Overview
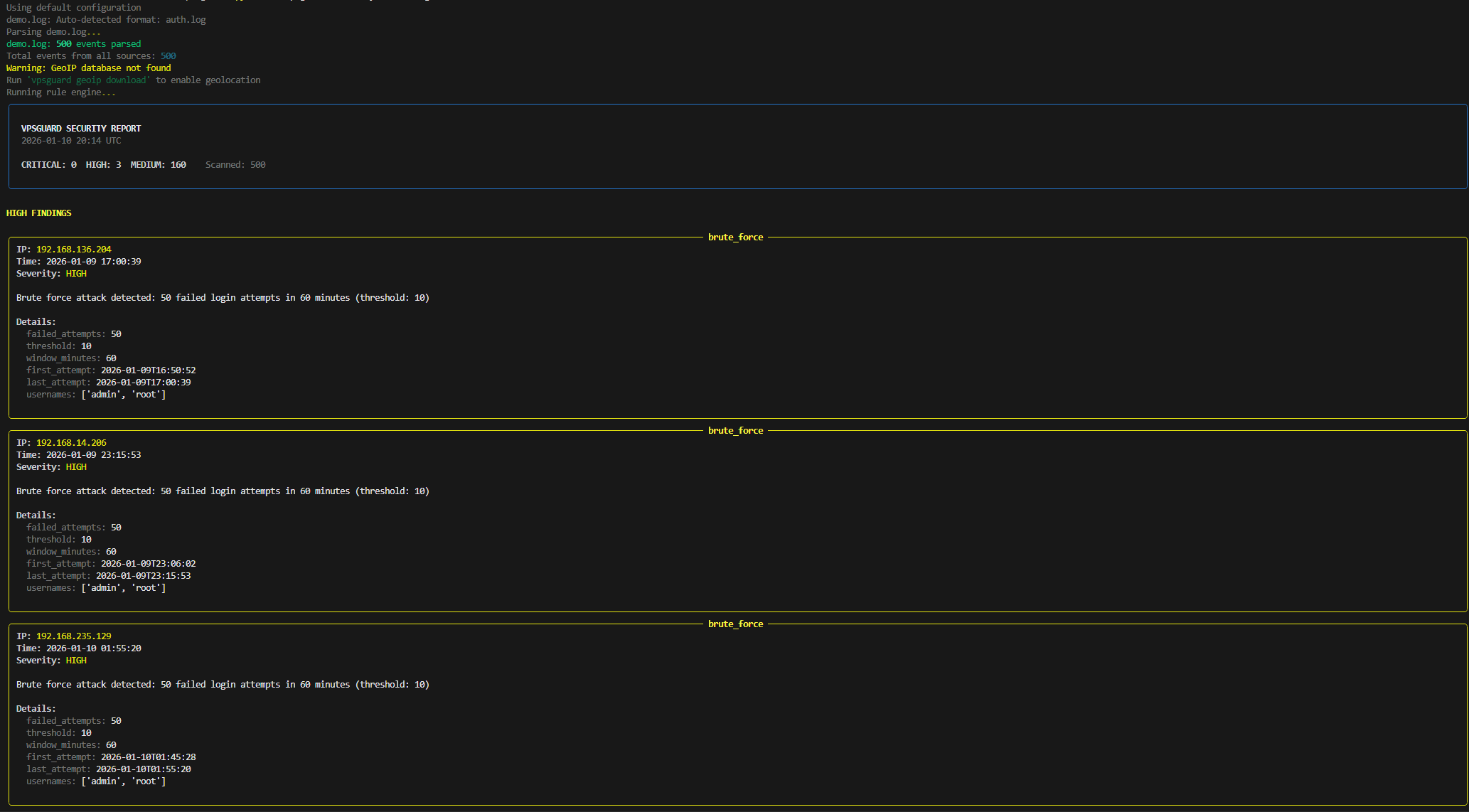
VPSGuard is an intelligent security analyzer for VPS authentication logs that combines traditional rule-based detection with machine learning to catch sophisticated distributed attacks. Unlike tools like fail2ban that rely solely on pattern matching, VPSGuard uses an IsolationForest ML model trained on clean baseline data to detect anomalous behavior patterns indicative of coordinated botnets, credential stuffing campaigns, and novel attack vectors. Features 7 detection rules, 5 log format parsers, GeoIP integration for geographic velocity detection, a watch daemon for continuous monitoring, and multiple output formats.
Problem
Traditional security tools like fail2ban use static rules that miss distributed attacks where individual IPs stay under thresholds but collectively pose a threat. Botnets, credential stuffing, and coordinated attacks evade per-IP detection.
Solution
Built a dual-detection system combining 7 configurable rules with an IsolationForest ML model. Rules catch known patterns while filtering flagged events from ML training data. The ML model learns normal baseline behavior and flags statistical anomalies, catching attacks that rules miss.
Architecture
Python CLI built with Typer and Rich for terminal output. Modular pipeline: Parsers normalize 5 log formats into AuthEvent objects; RuleEngine applies detection rules; MLEngine extracts 10 features per IP and runs IsolationForest anomaly detection; Reporters output to terminal, JSON, Markdown, or HTML. SQLite persistence for analysis history and watch state. Protocol-based abstractions enable extensibility.
Challenges
Designing ML features that capture distributed attack patterns (coordinated timing, username entropy, cross-source activity). Preventing baseline poisoning by excluding rule-flagged events from training. Building cross-platform log rotation detection for the watch daemon. Balancing sensitivity to catch real attacks without excessive false positives.
Results
Detects coordinated botnet attacks that fail2ban misses by analyzing temporal patterns and cross-IP correlation. Explainable anomaly scores show which features drove detection. Watch daemon enables continuous monitoring with configurable alert thresholds. 355 tests ensure reliability across parsers, rules, ML, and reporting.